Understanding the operational model of secondary fraud Rights Protection

In the world of cybercrime, scams come in many forms, each designed to exploit specific vulnerabilities in their victims. Recovery scams are a particularly insidious type of fraud that specifically targets individuals who have already suffered financial losses. This article examines how recovery scams work, explains their methods and target audience, and shows how to protect yourself.
What is a Recovery Scam?
Secondary recovery scams are fraudulent schemes in which scammers contact victims of previous scams and claim to be able to help them recover lost funds for a fee. These scams are particularly insidious because they exploit victims' desire and hope for compensation, often causing them further financial and emotional harm.
How do secondary recovery scams work?
Secondary recovery scams can be divided into several phases:
1. Victim Identification
Scammers typically obtain their victims' information through data leaks, online forums, or by even purchasing it from the original scammer. Furthermore, after defrauding a victim, the first scam center often sells their data to another scam center specializing in fraud involving alleged debt collection. Public complaints, comments, or pleas for help on social media can also lead to victims becoming targets of scammers.
2. Contacting Victims
Scammers typically contact their victims via email, telephone, or social media, impersonating employees of government agencies, law firms, or specialized debt collection companies. They often create fake law firm websites and write texts with a professional and legal-sounding tone to further deceive their victims. They use seemingly official names, fake certificates, and professional-looking websites to gain credibility.
3. Building Trust
To gain the victim's trust, scammers may:
Mention details of the original scam to appear legitimate.
Use technical jargon to seem more professional.
Claim to have successfully recovered funds for others.
Make false guarantees or assurances of success.
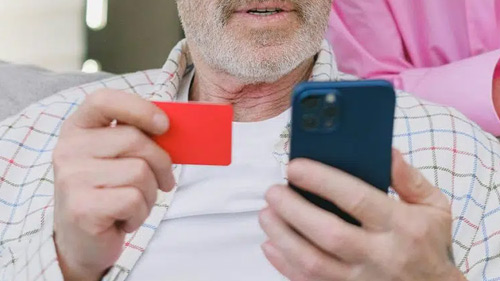
4. Requesting Payment
Once trust is established, scammers demand upfront payments or multiple fees, which they disguise as legal fees, taxes, or administrative costs. Under the guise of processing recovery efforts, they may also request sensitive information such as bank account details or identification documents.
5. Delaying Tactics
To extort as much money as possible, scammers may:
Provide fake status reports or documents purporting to demonstrate progress.
Claim unexpected complications requiring additional payments.
Threaten to halt the recovery process if the victim hesitates to pay.
6. Breaking Down Contact
Finally, the scammers break off contact with the victim, leaving them with further financial losses and no recovery of their funds.
Strategies and Warning Signs
Secondary fraud schemes often use the following tactics to manipulate victims:
Another tactic is the use of fake reviews and testimonials on platforms like YouTube. These reviews often contain phrases like "Thank you to [Name] for helping me recover my money" to create a false sense of legitimacy. Some scammers even impersonate well-known organizations like GASO and create fake profiles and success stories.
Pressure and Urgency: Scammers urge immediate action, claiming that delays could jeopardize the recovery process.
Emotional Manipulation: They exploit the victim's hopes and fears, hindering their critical thinking.
Impersonation of Authority: Scammers impersonate employees of financial regulatory authorities, law enforcement agencies, or reputable companies.
Exaggerated promises: Often, a full or guaranteed refund of funds is promised.
Warning signs:
Upfront payments are requested.
Unclear or unverifiable certificates.
Unsolicited contact from alleged recovery agents.
Requests for sensitive personal or financial information.
How to protect yourself from money scams
1. Check their credibility
Check the company or person contacting you.
Verify official registrations, reviews, or complaints.
Contact authorities or financial institutions directly to verify their legitimacy.
2. Be skeptical of guarantees
No reputable money recovery provider

Ivan A. Schlager
We understand the concerns and pressure that come with every case. Our professional team provides you with personalized legal consultation, quickly develops a plan to protect your rights, assists you in pursuing your claims, and safeguards your interests. Contact us now for a tailored solution.